 For an operating system and all of its services to run smoothly, the system clock has to be accurate. If it’s off by just a few seconds, the results could be disastrous. Read more
For an operating system and all of its services to run smoothly, the system clock has to be accurate. If it’s off by just a few seconds, the results could be disastrous. Read more


 For an operating system and all of its services to run smoothly, the system clock has to be accurate. If it’s off by just a few seconds, the results could be disastrous. Read more
For an operating system and all of its services to run smoothly, the system clock has to be accurate. If it’s off by just a few seconds, the results could be disastrous. Read more
 Just over two years have passed, or rather flown by, since the grand opening of the Tsvetochnaya 2 data center. In our article covering the event, we not only shared photos from the festivities, but briefly looked at the data center’s infrastructure. We soon started thinking that it’d be a great idea to publish a series of articles that take a more in-depth look at these systems. Well, we’ve finally managed to take a break from our day-to-day and put our plan into action.
Just over two years have passed, or rather flown by, since the grand opening of the Tsvetochnaya 2 data center. In our article covering the event, we not only shared photos from the festivities, but briefly looked at the data center’s infrastructure. We soon started thinking that it’d be a great idea to publish a series of articles that take a more in-depth look at these systems. Well, we’ve finally managed to take a break from our day-to-day and put our plan into action.
At the heart of it, the operations of any data center rest on three pillars: power, cooling, and security. Without a doubt, the key system here is power. Read more

 Despite how new something is or how long it’s been working under a full workload, equipment sometimes starts to act a bit unpredictably. Servers are no exception.
Despite how new something is or how long it’s been working under a full workload, equipment sometimes starts to act a bit unpredictably. Servers are no exception.
Crashes and malfunctions happen, and oftentimes, what should just be simple troubleshooting turns into a time-consuming whodunit.
Below, we’ll be looking at a few interesting and curious examples of how servers have misbehaved, and what was done to get them back in order. Read more

 The 11th annual HighLoad++ conference was held from November 7-8 at the Skolkovo Innovation Center. This year, the conference saw 2 700 people in attendance—200 more than last year! Today we’ll be reporting on the highlights and presentations that our team from Selectel saw. Read more
The 11th annual HighLoad++ conference was held from November 7-8 at the Skolkovo Innovation Center. This year, the conference saw 2 700 people in attendance—200 more than last year! Today we’ll be reporting on the highlights and presentations that our team from Selectel saw. Read more

 Are you ready for some big news? Cloud Storage has been fully updated and in some cases, service prices have been reduced threefold! Read more
Are you ready for some big news? Cloud Storage has been fully updated and in some cases, service prices have been reduced threefold! Read more
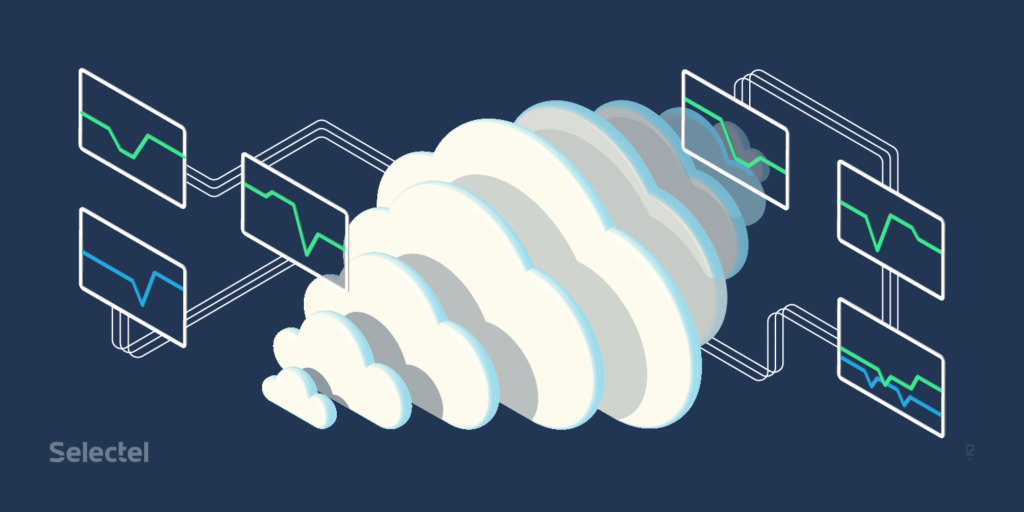
 We’ve added a new function to The Virtual Private Cloud to make managing virtual machines even more convenient and cost-effective: workload statistics.
We’ve added a new function to The Virtual Private Cloud to make managing virtual machines even more convenient and cost-effective: workload statistics.
Users can now view graphs on the workloads of virtual machine components from the control panel or gather measurement data over REST API.
In this article, we’ll talk about the components used for gathering, processing, and storing virtual machine metrics as well as give examples of how these components can be configured. Read more