
A few years ago, the Ostrovok.ru online hotel reservation service moved its infrastructure from the Amazon Web Services cloud to Selectel servers. The migration cost paid off in just a month, and the hosting expenses halved.
Read more

A few years ago, the Ostrovok.ru online hotel reservation service moved its infrastructure from the Amazon Web Services cloud to Selectel servers. The migration cost paid off in just a month, and the hosting expenses halved.
Read more
In a previous article in this series, dedicated to the Proxmox VE hypervisor, we already explained how to backup using built-in tools. This time, we’ll show you how to use the great Veeam® Backup&Replication™ 10 tool for the same purpose.
Read more

A truly bizarre reality seems to be unfolding with regard to the new fifth generation of wireless technologies. The 5G base stations are considered coronavirus carriers, weapons of mass destruction, and a major health threat with a capacity equivalent to dozens of microwave ovens. Let’s take a look at what lies behind the new technology and when we can expect the 5G symbol to appear on smartphone screens in Russia.
Read more

We share some tips from Olga Bagurina, HR specialist at Selectel, who joined the company three years ago as an intern and faced certain issues at the start. We talk about finding one’s calling, writing a compelling resume and a sincere cover letter, preparing for an interview, and some useful qualities for beginners.
Read more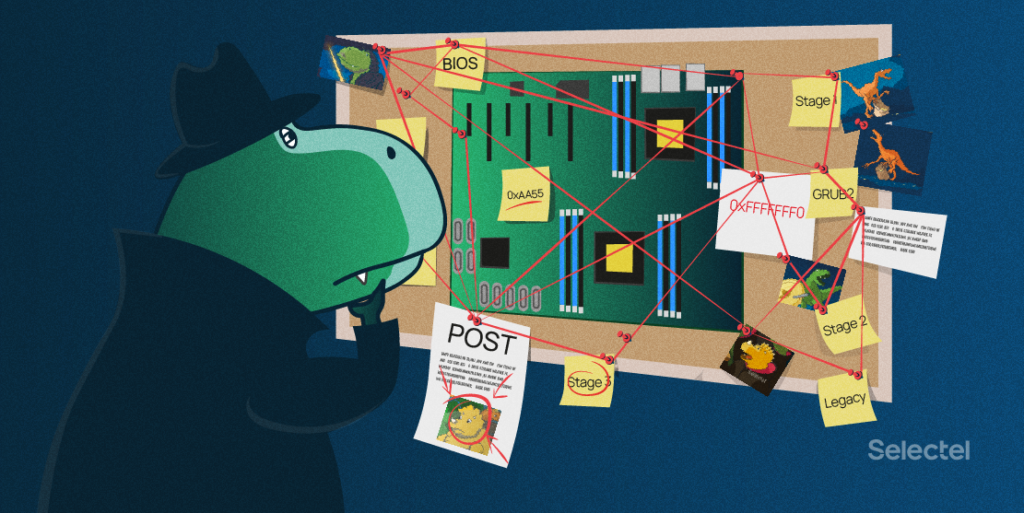
Even the most experienced and highly qualified system administrators often have only a vague idea of what exactly happens during the server startup process. So, let’s look at this process in detail.
Read more

Google Talk, Jabber, Slack, WhatsApp, Telegram, Zulip, Rocket.Chat, Selectel Chat… We are not rating messenger services, rather describing our journey to the ideal corporate tool.
You could also benefit from our experience: we changed our criteria several times and managed to successfully switch to new technological waves.
Read more